I recently enabled SAML authentication on Outlook Web App 2013, following the TechNet Documentation here: https://technet.microsoft.com/en-us/library/dn635116(v=exchg.150).aspx
It seemed to work fine; however, I would occasionally (about 1/8 attempts) receive an error message saying: “WrongAudienceUriOrBadSigningCert”
I had already added my ADFS token signing certificate to the Exchange server’s trusted root store as suggested here: https://flamingkeys.com/exchange-2013-with-ad-fs-login-fails-with-wrongaudienceuriorbadsigningcert/
The truly troubling thing was, that the issue could not be reproduced reliably. It affected both internal and external devices (both the primary ADFS and the ADFS Web Application Proxy servers)
I watched a fiddler trace as I attempted to access OWA, and the only difference between successful and failed attempts was a “/” at the end of the URL.
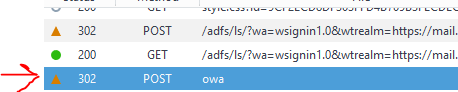
This can be observed in the POST body of the 302 to owa:
<saml:AudienceRestrictionCondition> <saml:Audience>https://mail.corp.org/owa/</saml:Audience> </saml:AudienceRestrictionCondition><saml:AudienceRestrictionCondition> <saml:Audience>https://mail.corp.org/owa</saml:Audience> </saml:AudienceRestrictionCondition>This is the token issued to me by my ADFS4 Server! It would seem that the tokens issued by the IdP do not contain a consistent Audience tag.
The TechNet documentation states very clearly that
The inclusion of the trailing slash / in the URL examples shown below is intentional. It’s important to ensure that both the AD FS relying party trusts and Exchange Audience URI’s are identical. This means the AD FS relying party trusts and Exchange Audience URI’s should both have or both emit the trailing slashes in their URLs. The examples in this section contain the trailing /’s after any url ending with “owa” ( /owa/) or “ecp” (/ecp/).
Ignoring this advise, I added all 4 urls to my Exchange farm configuration
$uris = @("https://mail.corp.org/owa/","https://mail.corp.org/ecp/","https://mail.corp.org/owa","https://mail.corp.org/ecp") Set-OrganizationConfig -AdfsIssuer "https://adfs.corp.org/adfs/ls/" -AdfsAudienceUris $uris -AdfsSignCertificateThumbprint "<thhumb>"Having 4 audience URIs resulted in a 100% success rate while attempting to open OWA from a successful ADFS authentication.
I hope this helps someone, as I couldn’t seem to find this issue anywhere else online.